Introduction
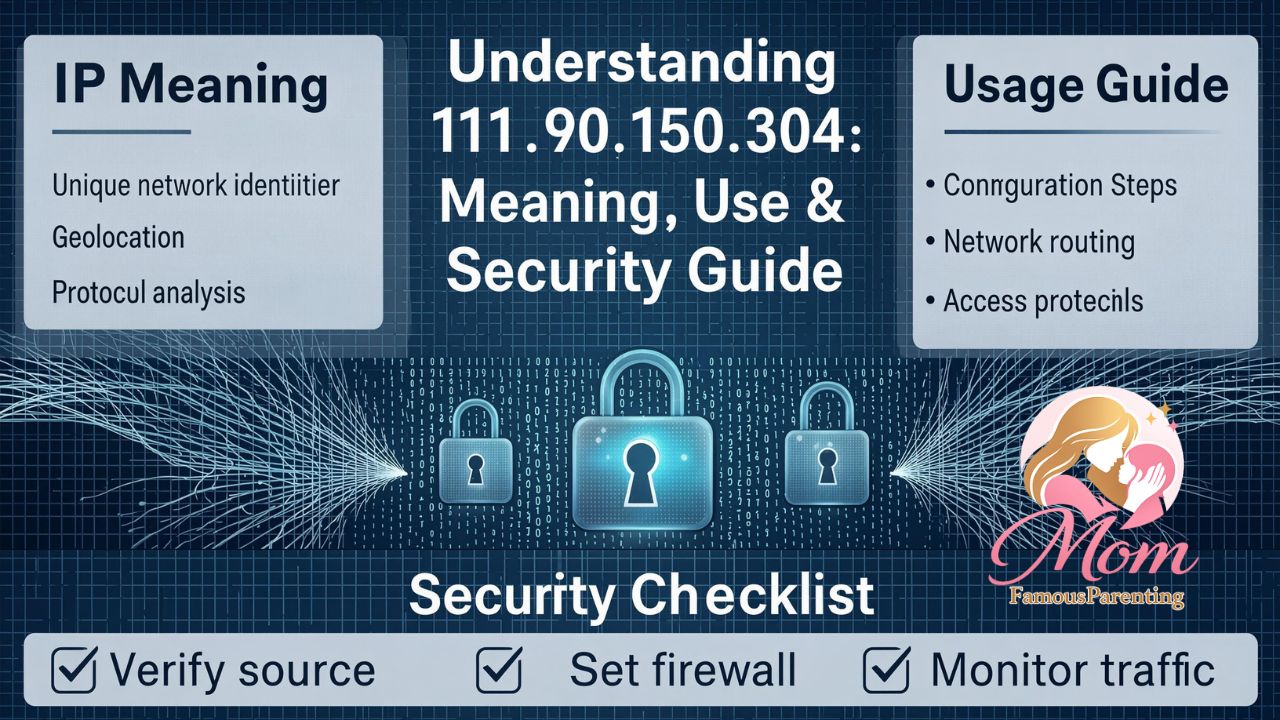
Every device connected to the internet carries a unique identifier, quietly guiding data across a vast global network. One such identifier—111.90.150.304—often appears in server logs, network monitoring tools, or hosting configurations, leaving many people wondering what it represents and why it matters.
Understanding 111.90.150.304 helps reveal how internet infrastructure works behind the scenes. Whether you are a website owner, developer, cybersecurity enthusiast, or simply curious about how the internet routes information, learning about IP addresses provides valuable insight into the digital ecosystem.
From hosting servers to website security and online privacy, IP addresses play a central role in connecting users, websites, and applications. This article explores what an IP address like 111.90.150.304 represents, how it functions within network systems, and why recognizing such identifiers can help protect digital platforms and improve internet awareness.
By the end, you’ll have a clear understanding of how addresses like 111.90.150.304 fit into the structure of the internet and why they occasionally appear in analytics reports, firewall logs, and hosting environments.

What Is an IP Address?
An IP address (Internet Protocol address) is a numerical label assigned to devices connected to a network that uses the Internet Protocol for communication. It functions as a digital address that allows computers and servers to locate each other across the internet.
Whenever a user visits a website, sends an email, or streams a video, data travels between devices using these numerical identifiers.
IP addresses serve three main purposes:
- Identifying devices on a network
- Enabling communication between servers and users
- Routing information across global internet infrastructure
In essence, every online interaction relies on IP addresses to ensure that information reaches the correct destination.
Understanding the Structure of 111.90.150.304
To understand 111.90.150.304, it helps to break down how IPv4 addresses are structured.
An IPv4 address typically consists of four numbers separated by periods, known as octets. Each section represents a portion of the address used for routing information through networks.
Example structure:
XXX.XXX.XXX.XXX
Each segment usually ranges from 0 to 255.
This format helps network devices quickly determine:
- The network where the device exists
- The specific device within that network
- How data packets should be routed
However, when examining 111.90.150.304, it is important to understand that valid IPv4 addresses typically range between 0–255 in each octet. This observation sometimes raises questions when such numbers appear in logs or URLs.
Why an Address Like 111.90.150.304 May Appear Online
There are several reasons why an identifier such as 111.90.150.304 might appear in analytics dashboards, hosting panels, or firewall logs.
1. Server Logging Systems
Web servers automatically log connection attempts. If a request includes malformed or unusual IP formatting, the server may still record it.
These logs help administrators detect:
- Suspicious traffic
- Automated bots
- Failed connection attempts
2. Proxy or Gateway Systems
Sometimes proxy servers or network gateways generate entries that appear similar to 111.90.150.304 during routing or traffic forwarding.
These entries may represent:
- Internal routing identifiers
- Gateway translations
- Network debugging data
3. Testing or Development Environments
Developers occasionally use placeholder IP addresses when testing applications or server configurations.
These placeholders simulate real-world network traffic while keeping systems isolated.
The Role of IP Addresses in Web Hosting
When someone visits a website, the domain name they type into a browser translates into an IP address through the Domain Name System (DNS).
This translation allows the browser to connect to the correct server hosting the website.
For example:
- A domain name like
example.com - Translates to a server IP address
- The browser then loads the website from that server
In hosting environments, administrators often monitor IP activity to track:
- Website traffic
- Security events
- Server performance
Seeing addresses such as 111.90.150.304 in logs may prompt administrators to verify whether the traffic is legitimate or unusual.
IP Address Lookup and Geolocation
IP lookup tools help identify the approximate location and ownership of an IP address.
These services analyze large databases that map IP ranges to:
- Internet service providers
- Hosting companies
- Data centers
- Geographic regions
However, IP geolocation is approximate, not precise. It generally identifies a region or network provider rather than an exact physical location.
Many online tools can perform an IP lookup and reveal information such as:
- ISP (Internet Service Provider)
- Hosting company
- Country or region
- Network organization
Such tools are widely used for cybersecurity investigations and website analytics.
Cybersecurity Implications of Unknown IP Addresses
Unknown IP addresses appearing in logs may indicate a variety of situations. While most internet traffic is harmless, administrators often investigate unfamiliar entries.
Potential causes include:
- Automated scanning bots
- Search engine crawlers
- Security vulnerability scans
- Failed login attempts
Monitoring addresses like 111.90.150.304 helps security teams detect patterns and identify potential threats.
Some organizations implement firewall rules that automatically block suspicious traffic originating from unfamiliar IP ranges.
IP Address Validation and Network Standards
Network standards ensure that IP addresses follow a consistent structure. Internet engineering organizations maintain these protocols to prevent routing conflicts and maintain stability across the global network.
A valid IPv4 address must:
- Contain four numerical segments
- Use numbers between 0 and 255
- Follow correct formatting rules
If a number exceeds these limits, the address may represent:
- An error in logging
- A testing placeholder
- An improperly formatted request
Therefore, when administrators encounter 111.90.150.304, they often verify whether the entry is legitimate or simply a formatting anomaly.
How Website Owners Monitor IP Traffic
Website administrators frequently monitor IP traffic using tools such as:
- Web server logs
- Analytics platforms
- Security monitoring systems
- Firewall dashboards
These tools allow site owners to identify unusual patterns, such as repeated requests from the same IP address.
Monitoring helps prevent issues like:
- Brute-force login attacks
- Spam submissions
- DDoS attempts
- Unauthorized access attempts
Understanding entries such as 111.90.150.304 allows administrators to maintain stronger control over server activity.
Privacy and Ethical Considerations of IP Tracking
While IP addresses provide valuable technical information, they also raise important privacy considerations.
An IP address alone does not identify a person directly, but when combined with other data sources it may contribute to digital profiling.
Many modern privacy regulations encourage responsible handling of IP data, including:
- GDPR in Europe
- Data protection laws in many countries
- Website privacy policies
Responsible organizations ensure that IP data is stored securely and used only for legitimate operational purposes.
Future of Internet Addressing: IPv6
The growing number of internet-connected devices has led to the development of IPv6, a newer addressing system designed to replace IPv4.
IPv6 uses a much larger address space and includes more complex formatting.
Example IPv6 format:
2001:0db8:85a3:0000:0000:8a2e:0370:7334
Advantages of IPv6 include:
- Vastly larger address capacity
- Improved routing efficiency
- Enhanced network security features
Despite these benefits, IPv4 remains widely used across the internet today.
FAQ
What is 111.90.150.304?
111.90.150.304 appears to be an IPv4-style address used in network logs or server monitoring systems. However, the final segment exceeds the typical IPv4 range.
Why might I see 111.90.150.304 in server logs?
It may appear due to malformed requests, testing environments, proxy systems, or logging anomalies within web server configurations.
Is 111.90.150.304 a real IP address?
Because IPv4 octets must range between 0 and 255, addresses exceeding that range may not represent valid public IP addresses.
Can an IP address reveal someone’s identity?
An IP address usually reveals only the network provider or approximate location, not the individual user.
How do websites track IP addresses?
Web servers automatically record IP addresses of incoming connections in access logs and analytics systems.
Should I block unknown IP addresses?
Not necessarily. Some unknown addresses belong to legitimate bots, search engines, or monitoring services.
How can I check where an IP address comes from?
IP lookup services and geolocation tools can estimate the provider and location associated with an IP address.
Are IP addresses permanent?
Some are static and remain constant, while others are dynamic and change periodically.
Conclusion
IP addresses are the foundation of how information travels across the internet. Identifiers such as 111.90.150.304 often appear in server logs, analytics reports, and network monitoring systems, prompting curiosity about their origin and purpose.
By understanding how IP addressing works, website owners, developers, and everyday internet users gain greater insight into the mechanics of digital communication. From routing data packets to identifying traffic sources, IP addresses quietly power every online interaction.
Recognizing unusual entries and understanding their context helps strengthen website security, improve network management, and deepen appreciation for the technology that connects billions of devices around the world.